GAMP-5 Mastery: Essential Guide to Computer System Validation for Regulated Industries
Table of Contents
GAMP-5 guidance, the related “V model” and the different software categories used to simplify the validation activities are nowadays considered the internationally recognised best approach for computer system validation. GAMP stays for “Good Automated Manufacturing Practice” and it is a guideline which is published by the ISPE, International Society for Pharmaceutical Engineering. The guideline is currently in Version 5.
Good Automated Manufacturing Practice, Founded in 1991. International Society for Pharmaceutical Engineering (ISPE) sets the guidelines for manufacturers and the current Version is GAMP 5. GAMP-5 is very important especially when the software application is provided by a supplier external to the organization. In fact this regulation requires users and suppliers to work together, each of them according to specific responsibilities, two gain the full validation of the software system.
Specifically, for the users, GAMP-5 provides a framework for validation activities to ensure that the system is fully validated according to its intended user before it moves to production. Suppliers, at the same time, can use GAMP to test the SW application for avoidable defects in the supplied system to ensure quality products are produced.
The origins of GAMP-5 trace back to 1991 when the ISPE established foundational principles to support manufacturers in implementing automated systems with robust quality controls. The GAMP-5 framework has since evolved into the authoritative reference for validating computer software in highly regulated industries. Its significance is especially pronounced when organizations utilize software supplied by external vendors. GAMP-5 emphasizes a collaborative validation approach where both users and suppliers share defined responsibilities to achieve full system validation. Users are guided by GAMP-5 to structure validation efforts, ensuring systems are thoroughly validated for their intended purpose before entering production. Simultaneously, suppliers leverage GAMP-5 to test software for preventable defects, confirming that the delivered system consistently supports product quality and regulatory compliance.
Computer system validation is essential for any quality management system related to medical devices, impacting different aspects such as 510k submission, MDSAP and much more.
COMPLETE CATALOG
Find the documentation you need — instantly.
Whether you need a complete kit or just one specific SOP, our catalog has it. 45 process packages and 3 complete bundles, all instantly downloadable and fully editable.
- ✓Complete bundles or individual packages
- ✓45 process packages from €69 each
- ✓ISO 13485 · MDSAP · Combined Kit
Why GAMP-5 Is Essential for Computer System Validation
The GAMP-5 guideline for computer system validation is founded on five core principles, which collectively provide a framework for ensuring the integrity, reliability, and regulatory compliance of computerized systems in regulated industries. Each principle serves as a cornerstone for a robust validation strategy:
- Leveraging Supplier Involvement: This principle highlights the critical role of suppliers in the validation process. Many computer systems depend on external vendors for software, components, or services. By fostering effective collaboration—through clear requirements, expectations, and communication—organizations can ensure that supplied systems meet quality, functional, and regulatory standards. A strong supplier partnership supports not only the initial validation but also the ongoing maintenance and compliance of the system.
- Product and Process Understanding: A deep understanding of both the product and its associated processes is essential for meaningful validation. This principle stresses that organizations must comprehend the product’s intended use, critical quality attributes, and the operational or manufacturing processes it supports. Such insight enables informed decisions regarding system design, qualification, and validation, ensuring that computerized systems align with the organization’s objectives and regulatory expectations.
- Lifecycle Approach within the QMS: Validation should follow a lifecycle-based methodology embedded within the organization’s Quality Management System (QMS). Activities must be planned, executed, and documented throughout the system’s entire lifecycle—from conception and development to deployment and retirement. This structured approach guarantees traceability, consistency, and compliance with regulatory requirements at every stage of the system’s life.
- Scalable Lifecycle Activities: Not all systems carry the same level of risk or complexity. This principle emphasizes that the scope and intensity of validation activities should be proportionate to the system’s impact on product quality, patient safety, and data integrity. By evaluating factors such as system complexity, criticality, and risk, organizations can allocate resources effectively, concentrating efforts where they are most needed while maintaining efficiency and avoiding unnecessary work.
- Science-Based Quality Risk Management: Integrating scientific, risk-based methodologies into validation is essential for proactively managing potential risks. This principle underscores the identification, assessment, control, and communication of risks associated with computerized systems. Implementing effective risk mitigation strategies enhances system reliability, ensures regulatory compliance, and safeguards patient safety, product quality, and data integrity.
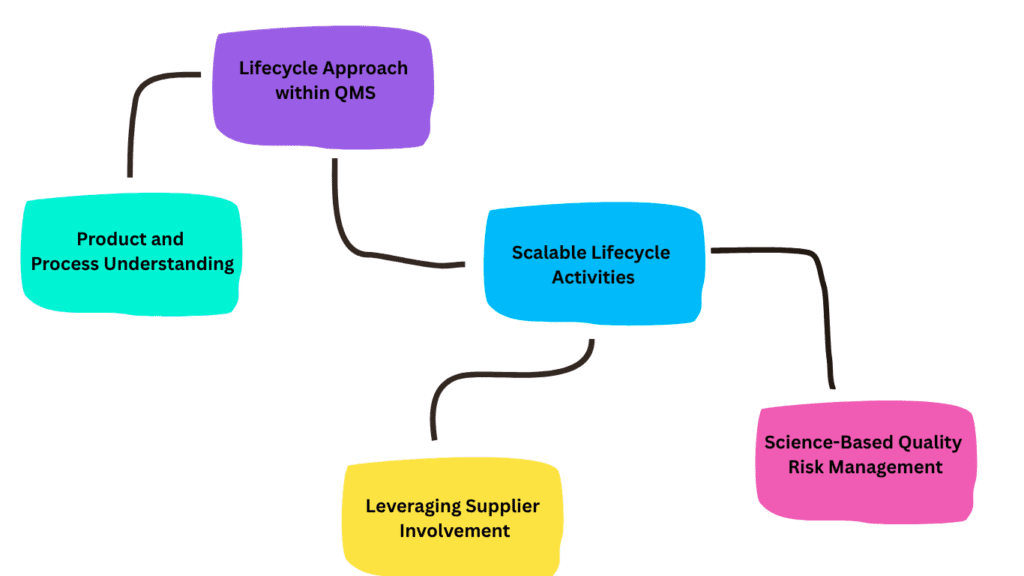
Together, these five principles provide a comprehensive foundation for GAMP-5–aligned validation, promoting efficiency, regulatory compliance, and confidence in the use of computerized systems.
Product and Process Understanding in Depth
In order to successfully conduct a validation activity, a comprehensive understanding of both the software product and its associated processes is imperative. The validation process culminates with the issuance of a “Fit for Use” statement, which can only be confidently provided if the most crucial functionalities of the product have been thoroughly comprehended and rigorously tested. These critical functionalities encompass aspects that significantly affect patient safety, product quality, and the security and integrity of data.
By delving deep into the intricacies of the software product, one can discern the functionalities that hold paramount importance in ensuring the overall success and effectiveness of the system. These critical functionalities act as the cornerstone for establishing a robust validation process. They encompass features and capabilities that, when functioning optimally, contribute directly to the safety and well-being of patients, the consistent delivery of high-quality products, and the protection of sensitive data.
Ensuring that the critical functionalities are comprehensively understood and rigorously tested is crucial for validating the software product’s suitability for its intended purpose. This involves a meticulous examination of how these functionalities interact with other system components, how they contribute to the overall product performance, and how they align with regulatory requirements and industry standards. Additionally, it necessitates conducting comprehensive testing to verify their reliability, stability, and accuracy under various operating conditions.
By focusing on the critical functionalities during the validation process, organizations can effectively mitigate risks associated with software failures or deficiencies that could have severe consequences for patients, product quality, and data security. It enables thorough scrutiny of these essential aspects, fostering a systematic approach to validation that ensures compliance with regulatory guidelines and industry best practices.
Ultimately, a successful validation activity hinges on the comprehensive understanding and meticulous testing of the critical functionalities within the software product. This approach empowers organizations to confidently assert the system’s fitness for use, assuring stakeholders that the product has been thoroughly evaluated and meets the highest standards of safety, quality, and data integrity.
Lifecycle Approach within QMS
The effective management of computer systems throughout their lifecycle is a critical aspect of the validation process, and it necessitates integration within the organization’s quality management system. As prescribed by the GAMP-5 methodology, this entails the establishment of a comprehensive Standard Operating Procedure (SOP) that outlines the management approach for each stage of the software application’s lifecycle.
By incorporating all phases of the software lifecycle into the quality system, organizations can demonstrate their commitment to ensuring adherence to defined requirements at each stage. This integration facilitates a seamless flow of activities, beginning from the conceptualization phase, where requirements are meticulously delineated, through to the subsequent stages of release, maintenance, and eventual retirement of the software.
During the concept phase, organizations must meticulously define and document the software’s functional and non-functional requirements. These requirements serve as a blueprint for the development and validation activities that follow. By explicitly outlining these requirements within the quality management system, organizations establish a robust foundation for the subsequent stages of the software’s lifecycle.
To effectively manage the release, maintenance, and retirement of the software, organizations must develop detailed SOPs that provide clear guidance and instructions for these specific stages. The release phase entails activities such as software installation, configuration, and documentation, which must be carried out systematically and in compliance with established procedures. Similarly, the maintenance phase encompasses ongoing support, bug fixes, and periodic updates to ensure the software’s continued functionality and reliability. Finally, the retirement phase necessitates proper decommissioning procedures, data migration or archiving, and the identification of any potential risks associated with the cessation of the software’s use.
By meticulously documenting and adhering to SOPs that encompass the entire software lifecycle, organizations can demonstrate their commitment to ensuring quality and regulatory compliance. This comprehensive approach provides a solid foundation for effective validation activities, as it ensures that all necessary requirements are defined, managed, and monitored throughout the software’s lifecycle.
Scalable Lifecycle Activities and the V Model
The planning and scaling of lifecycle activities for software validation can be approached from multiple perspectives, considering key parameters that influence the depth and scope of validation. These parameters include:
- Impact on Patient Safety, Product Quality, and Data Integrity: The degree to which a software application affects patient safety, product quality, or data integrity directly determines the rigor of validation required. A detailed risk assessment is performed to identify potential hazards and their consequences, allowing validation activities to be proportionate and focused on the highest-risk areas.
- System Complexity and Novelty: The complexity and innovativeness of a software application shape the validation strategy. Systems with intricate functionalities typically demand more comprehensive validation efforts. Similarly, novel technologies or unique features may require additional scrutiny to confirm their reliability, performance, and regulatory compliance.
- Supplier Assessment Outcomes: Evaluating the software supplier’s quality systems and compliance with regulatory standards informs the level of reliance placed on their deliverables. A supplier with robust quality practices may reduce the need for extensive validation, whereas gaps or uncertainties may necessitate more intensive verification activities.
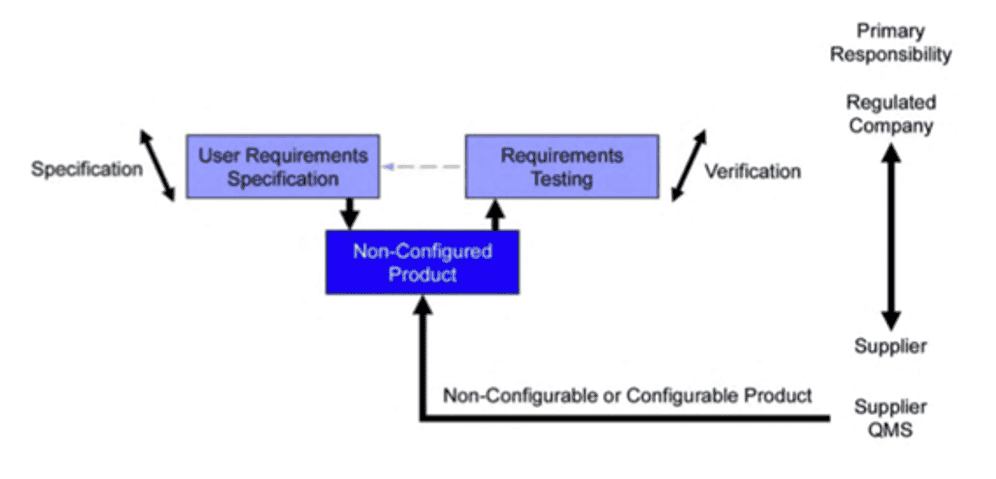
The V-model, widely recognized in GAMP-5, provides a structured framework for software lifecycle validation. Within this model, software applications are categorized according to GAMP-5 classifications, and validation efforts are tailored to the system’s complexity, risk, and intended use. For a detailed breakdown of these categories, refer to procedure P-06: Computer System Validation.
It is essential to understand that the V-model is flexible. GAMP-5 emphasizes that the type, scope, and depth of validation should be proportionate to the system’s risk profile, complexity, and supplier reliability, allowing organizations to align validation activities with both regulatory expectations and practical considerations. level of novelty and complexity, which, in turn, is reflected in the assigned GAMP-5 category.
Science-Based Quality Risk Management
The GAMP-5 framework emphasizes that validation efforts should concentrate on the most critical functions of a software application. Determining which functions are critical requires a risk-based approach, highlighting the necessity of fully understanding both the software and the processes it supports. This understanding is crucial for accurately assessing potential impacts on patient safety, product quality, and data integrity.
Applying a risk-based approach effectively involves a structured, stepwise methodology, which typically includes the following stages:
- Identify Critical Functions: Begin by pinpointing functions that directly affect patient safety, product quality, or data integrity. These functions are central to the application’s safe and compliant operation.
- Conduct Functional Risk Assessments: For each critical function, perform a thorough risk assessment. Evaluate potential hazards considering system behavior, data handling, and user interactions to understand the possible consequences of failures or errors.
- Implement and Verify Controls: Establish appropriate measures or controls to mitigate identified risks. Verification activities are essential to confirm that these controls are effective and sufficiently address the risks associated with each critical function.
- Ongoing Risk Review and Monitoring: Continuously monitor risks and the effectiveness of implemented controls throughout the software lifecycle. Regular reassessment allows the organization to detect new risks promptly, while ongoing monitoring ensures that existing controls remain effective and identifies areas needing adjustment or enhancement.
This systematic, risk-focused approach ensures that validation is not only thorough but also targeted, prioritizing the areas of highest impact and maintaining compliance with regulatory expectations throughout the software’s lifecycle.
Leveraging Supplier Involvement
Following the principles of GAMP-5, the ultimate responsibility for validating any software application rests squarely with the organization using it. That said, regulated companies can strategically leverage their suppliers’ existing documentation—including test protocols and results—to reduce redundant work and streamline the validation process. True validation effectiveness emerges when the organization and supplier collaborate closely, ensuring that efforts are focused, relevant, and aligned with regulatory expectations.
Utilizing supplier documentation offers a practical advantage: pre-existing test records can act as a foundation for the validation process. This not only conserves time and resources but also eliminates unnecessary duplication of work already performed by the supplier. By building on these materials, the organization can concentrate on validation tasks that require specific adaptation to their operational context and regulatory obligations.
Yet, depending solely on supplier documentation is insufficient. The organization must remain actively engaged in the validation process, contributing its own expertise and operational knowledge. A cooperative relationship with the supplier is essential to develop a shared understanding of the software’s intended use, functional requirements, and any organization-specific needs or concerns.
Through this collaboration, suppliers can offer critical insights into software performance, functionality, and potential risks, while helping to clarify ambiguities in documentation. Such joint effort ensures that validation is not only thorough but also accurately reflects the software’s capabilities and limitations. The result is a higher-quality, more reliable validation outcome that is tailored to the organization’s unique context.
Central to this process is open, transparent communication between the supplier and the organization, which underpins the effectiveness and integrity of the entire validation exercise.
MULTI-MARKET KIT
One audit. Five markets. Ready to submit.
Our MDSAP Documentation Kit covers Brazil ANVISA, Japan PMDA, Canada Health Canada, Australia TGA, and FDA — with country-specific reportability worksheets and application checklists you can use today.
- ✓15 SOPs covering 5 MDSAP markets
- ✓18 templates with country worksheets
- ✓Brazil · Japan · Canada · Australia · USA
Conclusion: Why GAMP-5 Remains the Gold Standard for Computer System Validation
In today’s highly regulated environment, adopting a structured and risk-based approach to computer system validation is no longer optional—it is essential. The GAMP-5 framework, with its well-established principles, scalable lifecycle model, and emphasis on risk management, provides organizations with a clear and internationally recognized pathway to achieve compliance and ensure system reliability.
By integrating the V-model, leveraging supplier involvement, and applying science-based quality risk management, companies can significantly improve the efficiency and effectiveness of their validation activities. This approach not only reduces unnecessary effort but also ensures that critical functions impacting patient safety, product quality, and data integrity are thoroughly controlled and verified.
Moreover, GAMP-5 promotes a modern validation mindset—focused on understanding processes, managing risks, and optimizing resources—which is perfectly aligned with current regulatory expectations, including EU MDR, FDA 21 CFR Part 11, and global quality standards.
Ultimately, organizations that implement GAMP-5 principles within their Quality Management System are better equipped to demonstrate compliance, streamline audits, and maintain robust, reliable computerized systems throughout their lifecycle. For any company operating in the medical device or pharmaceutical sector, GAMP-5 is not just a guideline—it is a strategic advantage for achieving sustainable compliance and operational excellence.