IEC 81001-5-1: The Complete Guide to Cybersecurity for Health Software
Table of Contents
Introduction
IEC 81001-5-1 cybersecurity for health software has become one of the most referenced standards in the medical device and digital health regulatory landscape. As connected health systems proliferate — from cloud-based clinical decision support tools to networked hospital devices — the need for a structured, internationally recognized cybersecurity framework has never been more urgent.
This article provides a comprehensive guide to IEC 81001-5-1: its scope, relationship to other key standards, core requirements, practical implementation approach, and regulatory relevance across major markets including the EU and the US. It is part of our ongoing series on medical device software regulation, alongside our articles on IEC 62304 and SOUP management.
What Is IEC 81001-5-1?
IEC 81001-5-1 is an international standard published by the International Electrotechnical Commission (IEC) as part of the broader IEC 81001 series, which addresses safety, effectiveness, and security of health software and health IT systems. Specifically, Part 5-1 focuses on cybersecurity activities in the product lifecycle — defining what manufacturers and developers of health software must do to identify, assess, and control cybersecurity risks throughout the entire software lifecycle, from initial design through post-market maintenance.
The standard applies to:
- Manufacturers of medical device software — including Software as a Medical Device (SaMD) and software embedded in medical devices
- Developers of health IT systems — clinical information systems, electronic health records, hospital information systems
- Healthcare providers deploying and operating health software in clinical environments
- Regulatory affairs and quality teams responsible for cybersecurity compliance documentation
IEC 81001-5-1 is designed to complement — not replace — other key standards in the medical device ecosystem. It works alongside IEC 62304 (software lifecycle processes), ISO 14971 (risk management), and ISO/IEC 27001(information security management), creating a coherent and integrated framework for safe and secure health software development.
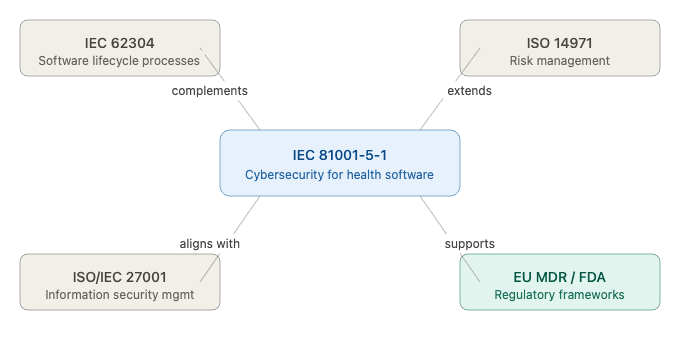
Figure 1 — IEC 81001-5-1 and its relationship to other key standards
Why IEC 81001-5-1 Matters — The Cybersecurity Case for Health Software
The healthcare sector has become one of the most targeted industries for cyberattacks globally. Ransomware attacks on hospitals, data breaches of electronic health records, and vulnerabilities in connected medical devices have all demonstrated that cybersecurity failures in health software are not just an IT problem — they are a patient safety problem.
Regulatory bodies have responded decisively. The FDA’s 2026 Cybersecurity Guidance for medical devices makes cybersecurity documentation a mandatory element of premarket submissions. The EU MDR 2017/745 requires manufacturers to address cybersecurity as part of the general safety and performance requirements under Annex I, Chapter II. The NIS-2 Directive extends cybersecurity obligations across the broader healthcare supply chain.
IEC 81001-5-1 provides the technical and process framework that allows manufacturers to demonstrate compliance with these regulatory expectations in a structured, auditable, and internationally recognized way. It is the standard that translates regulatory cybersecurity obligations into specific engineering and quality management activities.
COMPLETE CATALOG
Find the documentation you need — instantly.
Whether you need a complete kit or just one specific SOP, our catalog has it. 45 process packages and 3 complete bundles, all instantly downloadable and fully editable.
- ✓Complete bundles or individual packages
- ✓45 process packages from €69 each
- ✓ISO 13485 · MDSAP · Combined Kit
Scope and Structure of IEC 81001-5-1
IEC 81001-5-1 is organized around the concept of a Security Development Lifecycle (SDL) — a structured set of cybersecurity activities that must be integrated into every phase of the software lifecycle, from planning and design through release, post-market maintenance, and eventual decommissioning.
The standard defines requirements across six core areas:
- Initiation — establishing cybersecurity governance, roles, and responsibilities
- Requirements — defining security requirements alongside functional requirements
- Design — integrating security architecture and threat modeling into software design
- Implementation — applying secure coding practices and security testing
- Verification and validation — confirming that security controls work as intended
- Post-market — monitoring threats, managing vulnerabilities, and issuing patches after release
This lifecycle structure mirrors and integrates directly with the software lifecycle processes defined in IEC 62304, ensuring that cybersecurity activities are embedded within the existing software development framework rather than added as a separate afterthought.
Key Requirements of IEC 81001-5-1
1. Cybersecurity Risk Management
IEC 81001-5-1 requires manufacturers to integrate cybersecurity risk management throughout the product lifecycle, using a methodology aligned with ISO 14971. This means identifying cybersecurity threats and vulnerabilities, assessing the likelihood and impact of exploitation, and implementing risk controls proportionate to the identified risk.
A key distinction from traditional safety risk management is the concept of threat modeling — a structured analysis of potential adversarial attacks against the software system. Threat modeling must be performed early in the design phase and updated as the system evolves. Common methodologies referenced in industry include STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) and PASTA (Process for Attack Simulation and Threat Analysis).
2. Security Requirements Specification
Security requirements must be explicitly defined and documented alongside functional software requirements. These include both technical security requirements — such as encryption standards, authentication mechanisms, and session management policies — and organizational security requirements — such as user access policies and incident response procedures.
Security requirements must be traceable to identified threats and risk controls, and must be verifiable through testing. This traceability is a key element that auditors and regulators will examine during technical file reviews.
3. Secure Development Practices
IEC 81001-5-1 requires manufacturers to apply secure coding principles throughout the implementation phase. This includes following established guidelines such as OWASP (Open Web Application Security Project) secure coding practices, applying the principle of least privilege in software architecture and access control, performing software composition analysis to identify vulnerabilities in third-party components (directly linking to SOUP management under IEC 62304), and conducting regular code reviews with a security focus.
4. Security Testing and Verification
The standard mandates a structured security testing program that must include:
- Static Application Security Testing (SAST) — automated analysis of source code for security vulnerabilities
- Dynamic Application Security Testing (DAST) — testing of running applications for exploitable vulnerabilities
- Penetration testing — simulated adversarial attacks to identify weaknesses not detected by automated tools
- Fuzz testing — automated generation of malformed or unexpected inputs to test system resilience
Security testing results must be documented and traceable to the security requirements and threat model.
5. Vulnerability Management and Patch Management
One of the most practically demanding requirements of IEC 81001-5-1 is the obligation to maintain an active vulnerability management process throughout the product’s commercial lifetime. This requires continuously monitoring vulnerability databases (including the CVE database and vendor security advisories), evaluating newly disclosed vulnerabilities against the device’s threat model and risk profile, developing and deploying security patches through a controlled change management process, and communicating with customers and regulators about identified vulnerabilities and available mitigations.
6. Incident Response
Manufacturers must establish and maintain a documented cybersecurity incident response plan that defines roles and responsibilities, detection and escalation procedures, containment and remediation actions, and communication obligations — including regulatory reporting requirements under EU MDR and FDA regulations.
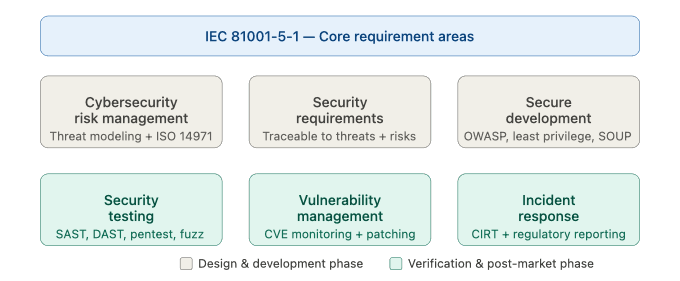
Figure 2 — Core requirement areas of IEC 81001-5-1
IEC 81001-5-1 and the Security Development Lifecycle
The most practical way to understand IEC 81001-5-1 is through its Security Development Lifecycle (SDL) model — the sequential integration of cybersecurity activities into each phase of software development. Unlike a checklist approach, the SDL model ensures that security is built into the product from the beginning rather than assessed at the end.
Planning phase: Define the cybersecurity scope, identify assets requiring protection (patient data, device configuration, clinical algorithms), assign roles and responsibilities for cybersecurity activities, and establish the threat modeling methodology to be used.
Requirements phase: Elicit and document security requirements derived from the threat model and risk assessment. Define security acceptance criteria that will be used during verification. Ensure security requirements are captured in the same requirements management system as functional requirements, with bidirectional traceability.
Design phase: Perform threat modeling using a structured methodology. Design security architecture — including authentication mechanisms, encryption strategies, network segmentation, and audit logging. Document security design decisions and their rationale.
Implementation phase: Apply secure coding standards. Perform code reviews with a security focus. Conduct software composition analysis to identify vulnerabilities in third-party dependencies — a direct interface point with SOUP management under IEC 62304.
Verification phase: Execute the full security testing plan including SAST, DAST, penetration testing, and fuzz testing. Document all findings and their remediation. Verify that all security requirements have been met and that the residual cybersecurity risk is acceptable.
Post-market phase: Monitor the cybersecurity landscape continuously. Evaluate newly disclosed vulnerabilities. Issue patches through a controlled process. Communicate with customers and regulators as required. Update the threat model and risk assessment when significant changes occur in the threat landscape or in the device itself.
Regulatory Alignment — EU, US, and Beyond
IEC 81001-5-1 has been designed with explicit consideration of major regulatory frameworks, making it a highly effective tool for demonstrating cybersecurity compliance across multiple markets simultaneously.
European Union (EU MDR 2017/745): Annex I, Chapter II of the MDR requires that devices incorporating software — or software that is a device in itself — be designed and manufactured in accordance with the state of the art in security. The MDCG guidance documents on cybersecurity (particularly MDCG 2019-16 Rev. 2) explicitly reference IEC 81001-5-1 as a means of demonstrating compliance. Notified bodies are increasingly expecting manufacturers to reference this standard in their technical documentation.
United States (FDA): The FDA’s 2023 Cybersecurity Guidance for Medical Devices requires manufacturers to include cybersecurity documentation in premarket submissions, including a Software Bill of Materials (SBOM), a cybersecurity risk management framework, and evidence of security testing. IEC 81001-5-1 provides a recognized framework for satisfying these requirements.
International markets: Canada (Health Canada), Australia (TGA), and Japan (PMDA) are all increasingly aligning their cybersecurity expectations with international standards including IEC 81001-5-1, making compliance with this standard a strong foundation for multi-market regulatory strategy.
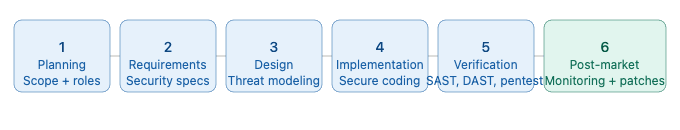
Figure 3 — IEC 81001-5-1 Security Development Lifecycle
Practical Implementation — How to Achieve IEC 81001-5-1 Compliance
Start with a Cybersecurity Gap Analysis
Before implementing IEC 81001-5-1, organizations should perform a structured gap analysis comparing their current practices against the standard’s requirements. Key questions to address include: Is cybersecurity currently integrated into your software development process or handled as a separate afterthought? Do you have a documented threat modeling methodology? Is there a formal vulnerability monitoring and patch management process post-release?
The gap analysis output should feed directly into a Cybersecurity Implementation Plan that prioritizes the most critical gaps based on their risk impact.
Integrate Cybersecurity into the Quality Management System
IEC 81001-5-1 compliance cannot be achieved through engineering activities alone — it requires documented procedures integrated into the Quality Management System (QMS). Under ISO 13485, manufacturers must ensure that their QMS covers software-related activities. Cybersecurity procedures — covering threat modeling, security testing, vulnerability management, and incident response — should be part of the QMS documentation structure, not standalone engineering documents.
Invest in Threat Modeling Capability
Threat modeling is the activity that underpins the entire IEC 81001-5-1 framework, yet it is the area where most organizations have the most significant capability gap. Building internal competence in threat modeling — or engaging experienced external support — is the single most impactful investment manufacturers can make for IEC 81001-5-1 compliance.
Leverage the SBOM for Post-Market Vulnerability Management
The Software Bill of Materials (SBOM) — already a requirement under modern FDA and EU MDR cybersecurity expectations — is the operational foundation of post-market vulnerability management. Without a complete, up-to-date SBOM, it is not possible to rapidly identify which devices are affected when a new vulnerability is disclosed. The SBOM should be generated automatically using Software Composition Analysis tools and maintained in version control alongside the software itself.
Document Everything with Traceability in Mind
Regulators and notified bodies reviewing cybersecurity compliance under IEC 81001-5-1 will expect to see full traceability from identified threats → security requirements → design decisions → security test results → residual risk acceptance. This traceability matrix is the primary audit artifact — building it from the start of the project is far less costly than reconstructing it after the fact.
Common Mistakes in IEC 81001-5-1 Implementation
Treating cybersecurity as a pre-submission activity: Cybersecurity cannot be retrofitted at the end of development. Organizations that begin threat modeling and security testing only when preparing for regulatory submission will face significant rework and delays.
Confusing IT security with product security: IEC 81001-5-1 focuses on the security of the health software product itself — not the manufacturer’s internal IT infrastructure. While both are important, they require different approaches and are governed by different standards.
Neglecting post-market obligations: Many manufacturers focus on achieving pre-market cybersecurity compliance and underestimate the ongoing post-market obligations — continuous vulnerability monitoring, patch management, and regulatory reporting. These activities require dedicated resources and processes that must be established before product launch.
Inadequate supplier and SOUP management: Third-party components are a primary source of cybersecurity vulnerabilities in health software. Failing to maintain an up-to-date SBOM and monitor SOUP components for newly disclosed vulnerabilities is one of the most common — and most serious — compliance gaps.
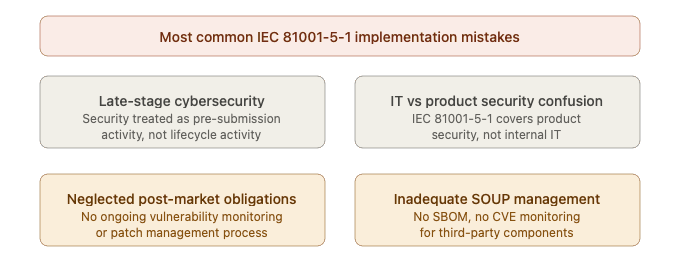
Figure 4 — IEC 81001-5-1 common implementation mistakes
Future Trends in Health Software Cybersecurity
The cybersecurity landscape for health software is evolving rapidly, and IEC 81001-5-1 is designed to be a living framework that evolves alongside it. Several emerging trends will shape how manufacturers implement and maintain cybersecurity compliance in the coming years.
AI-driven threat detection is increasingly being applied to health software security monitoring, enabling real-time identification of anomalous behavior that may indicate a cyberattack. As AI-based medical devices become more prevalent, the intersection of AI safety and cybersecurity will require new approaches to threat modeling and risk assessment.
Zero-trust architecture is replacing traditional perimeter-based security models in health IT environments. Under a zero-trust model, no user or system component is trusted by default — every access request must be authenticated and authorized, regardless of its origin. This architectural approach significantly reduces the attack surface in connected health systems.
Quantum-resistant cryptography is becoming an active area of regulatory attention. Current encryption algorithms are vulnerable to future quantum computing attacks, and forward-looking manufacturers are beginning to design cryptographic agility into their systems — the ability to upgrade cryptographic algorithms without major architectural changes.
Supply chain security has moved to the top of the regulatory agenda following high-profile software supply chain attacks. The SBOM is the foundational tool for supply chain visibility, and regulators are increasingly expecting manufacturers to demonstrate not just what SOUP components they use, but that those components come from verified, trustworthy sources.
COMPLETE CATALOG
Find the documentation you need — instantly.
Whether you need a complete kit or just one specific SOP, our catalog has it. 45 process packages and 3 complete bundles, all instantly downloadable and fully editable.
- ✓Complete bundles or individual packages
- ✓45 process packages from €69 each
- ✓ISO 13485 · MDSAP · Combined Kit
Conclusions
IEC 81001-5-1 represents the most comprehensive and internationally recognized framework for cybersecurity in health software available today. By providing a structured Security Development Lifecycle that integrates seamlessly with existing medical device standards — IEC 62304, ISO 14971, and ISO/IEC 27001 — it enables manufacturers to address cybersecurity not as a regulatory hurdle, but as a fundamental dimension of product quality and patient safety.
The practical message for medical device and health software manufacturers is clear: cybersecurity compliance under IEC 81001-5-1 cannot be achieved through documentation alone. It requires genuine integration of security engineering practices into every phase of the product lifecycle — from threat modeling at the design stage through vulnerability monitoring and patch management throughout the commercial lifetime of the device.
Manufacturers who invest in building these capabilities now — rather than retrofitting them under regulatory pressure — will be better positioned for faster regulatory submissions, more confident audit outcomes, and ultimately safer products for the patients who depend on them.
This article is part of the MD Regulatory series on medical device software regulation. Related articles in this series cover IEC 62304 software safety classification, SOUP management, and cybersecurity risk assessment for medical devices.



4 Comments
Comments are closed.